I blog about anything I find interesting, and since I have a lot of varied interests, my blog entries are kind of all over the place. You can browse my tags to sort them by topic and see which ones I frequently write about, or the archive has a complete history of my posts, dating back to 2008!
Besides my blog, I have pages for my creative projects, which are linked to on the navigation bar.
I write a lot about Linux and Android, Minecraft, and I like to rant about stuff. Generally anything that makes me curious. Also check out my Bookmarks for all sorts of cool websites about various topics I'm interested in.
For the geeks: this website respects your privacy and doesn't run any third party ads or analytics. This site speaks HTTP and doesn't require any JavaScript to work.
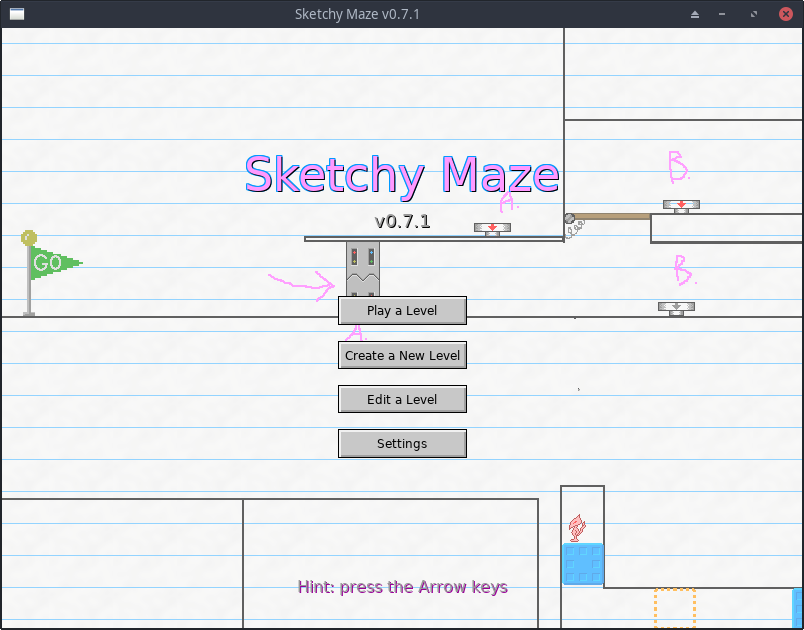
Sketchy Maze v0.7.1It's been a while since I last wrote about my videogame project, Project: Doodle, which has now been given a proper name: Sketchy Maze. There have been a few releases of the game since I last wrote about version 0.4.0 and they bring some exciting new features!
On forums like r/privacy people often discuss the role of open source software when it comes to privacy and end-to-end encrypted messaging applications. The general consensus is: a privacy focused app must be open source so that people can get their eyes on the source code and audit it for security vulnerabilities, verify it's doing what it says in the tin and without any secret government backdoors built in that would undermine the security and reveal peoples' private chats.
These are all well and good: if the source code is not open, you can't verify the code isn't doing something sneaky like uploading your encryption keys to the service provider or whatever. But, open source alone isn't a silver bullet to help guarantee the security of the app:
In this post I'll address a few common tired things I hear people on r/privacy say in regards to this topic and how it's never quite that simple.
Have you ever wondered basically how blockchains work and what it means to "mine a Bitcoin" and why it's a time-consuming (and energy-intensive) process to mine one? In this blog post I'll summarize what basically drives blockchains and how they work, from my understanding of them anyway.
If you're anywhere close to a novice web developer or have ever hashed a password in your life, you already know the basic technology at play here. And even if you haven't, I think I can get you caught up pretty quickly.
The explanation I give below is surely super simplified and is based on my reading of how these work, along with several "Create your own blockchain in under 200 lines of code" type of tutorials which you could find for Python, or JavaScript or anything. It doesn't cover how the decentralized networking aspects work or any of those details, but just the basics on the cryptography side.
Among my many diverse interests, one thing that fascinates me is to contemplate the nature of the universe and what Reality is made of, or at least, what my perception of Reality is made of and how the inner mind works.
To that end, topics such as quantum physics, simulation theory, and esoteric writings from the world's oldest religions like Hinduism and Gnosticism are interesting to me, and I like to talk crazy about that sort of thing from time to time.
In this post, though, I'm going to write strictly about visual perceptions that I've experienced at different times in my life. Many are related to psychotropic compounds, including cannabis, but now I'm able to experience some crazy things just by meditating while sober too.
The other day, quite by accident, I learned how to enter a fully "tripping balls" state of mind, while completely sober, purely by meditating and staring blankly out into space.
All I was trying to do was meditate, and keep my mind shushed and quiet, for as long as I could manage to, and push to set a new personal record for myself. I'd been practicing meditation for a couple of years, since my spiritual awakening in 2018. So I was just focused on keeping my mind still, but kept my eyes open, and was staring blankly out at the walls of my apartment, which had a complex surface to them.
Complex surface? By this I mean, my walls had a sort of "sprayed on" finish to them, similar to ceilings in many homes, so instead of a smooth finish or tiles or w/e, the wall is 'chaotic' and messy, with ridges and dents and lines and complexity. Any complex surface will do.
So I was just staring, focused on a single point on the wall, mind still, and I kept this up even while my visual perception began to fall apart (as it does due to the sensory tolerance of staring at the same image for so long -- this much I knew would happen even from my early childhood when I'd zone out and daydream while staring at trees or things). It is a bit hard to pull off, I get a strong urge to blink or move my eyes when my perception begins to fall apart, but with some practice you can power through this part.
What happened next is where it started to get interesting.
You know those "closed eye" visuals you get when your eyes are shut? Random colors and blobby shapes and so on. Well, I began to see these same sorts of visuals while my eyes were open. They were overlaid on top of the image of the wall I was staring at. Only then, instead of the colorful blobs doing their own thing, they started to "play off of" the patterns on the wall; they'd cling to the ridges and edges, and make the details on the wall begin to wiggle a bit, interacting with it instead of the blobs simply doing their own (usual) thing over top.
Eventually from the colored visuals emerged some fractal-like patterns, and before too much longer, the visuals came to reach full-on 'tripping balls' territory, like the peak of a psychedelic trip on mushrooms or similar. Rainbow colors washing over the wall, every little detail is wiggling and dancing around, fractal patterns, and even these tiny details I didn't even notice were there emerged and those were wiggling and moving around too. If you've dabbled in psychedelics, you know what I'm talking about, only no such substances were necessary: I meditated my way into seeing this stuff. I didn't even expect this was possible!
And as soon as I'd look away? Gone. Back to normal, nothing wiggling around anymore, Reality is back in its place.
Now, the first time I pulled this off, I had smoked a single hit of cannabis, as I do many days of the week (it's legal for adults in Oregon). But when I pulled this off, nothing about the experience felt related to the weed in particular, and that I should be able to do this while completely sober, and can bring on these visualizations at will any time I choose.
The next day I tested exactly this: no weed, no nothing, just laid on my bed and stared at my ceiling while meditating and waited for the visuals to come on.
Try it yourself, I'm curious if others can turn up the same results.
- Meditate, trying to keep your mind quiet, turn off noisy chatter. This may take some practice. If you're a beginner, just meditate by focusing on your breath, and breathe in and out; don't control your breath, just watch it, and if your mind wanders, and you realize you've wandered, just come back to your breath and keep trying, don't beat yourself up for it.
- Do this while staring at a fixed point in the room, preferably on a complex surface. Don't blink or look away even while your visuals begin to do weird things; power through it.
- Don't focus on seeing trippy visuals as a goal; when I thought too much about seeing visuals, they wouldn't come on, I'd have to just focus on keeping my mind quiet, and the visuals happen naturally.
While I was "meditation tripping," I thought to myself, "is this what people mean when they talk about 'flashbacks' where you get psychedelic visuals later in life after you've used these substances once before?" -- it fully, 100% looked like height-of-the-trip visuals. But, they were completely under control, in that I willed myself into it, and they were gone like *snap* as soon as I looked away.
The visuals were always my favorite part of psychedelics, anyway, and I can do without the "ego death" and the "impressionable mind" aspects of a trip. As I continue my meditation practice, now I know how I can give myself a laser light show to watch while at the same time extending my tolerance for keeping my mind still and quieted.
This story is related to the above which will become clear after a while.
So, I'd been using cannabis since about 2016 and all was normal and fine for a while, but in the last couple of years especially, very often after I'd smoke I would start to see a sort of "hexogonal pattern" emerge over my view of Reality.
It was like a 2D honeycomb texture overlaid on top of all the 3D things I was seeing in my space; sort of like the pixels you see if you look really closely at a computer screen. Or like, it was as though 3D reality was actually a projection onto a flat 2D surface and that this hexogonal honeycomb pattern were the "pixels" that make Reality function.
They were especially noticeable when I'd look at a bright white computer screen, like the background of most web pages, because the solid white color removes all visual distraction and I could see the honeycomb pattern the most clearly.
I can't really say what color the hexagon pattern is, as the whole thing seems to flash colors like red and blue, like TV static, but the static is structured and organized into a clear pattern.
If I was reading some text on my screen, the letters would wiggle and interact with the hexagons where the letter touched a border between two cells. It's pretty reliable for me to see this pattern pretty much any time I smoke weed now.
One of the first times I noticed this pattern, I was curious about it and tried to focus and see it more clearly and figure out what it was. I was staring at my white computer screen as it was the easiest to distinguish the pattern on, and as I focused on it, it was like the veil of Reality began to disintegrate and fall apart, like "holes" appeared in my monitor and I could see "through" reality to get a better look at what was behind it.
What I began to see, though, frightened me and I stopped. I had seen it, in all its terrifying glory, once before in my life - story below.
How it relates to meditating myself into tripping? The earlier parts of the visuals I was seeing started out much the same as this hexogonal pattern, before it changed and became fractals and making the wall dance around. I feel the two are the same phenomenon in different forms.
So, going all the way back to my very first time smoking weed, in 2013 or 2014 or so. I tried it the first time, and I fully tripped balls and left reality all together, with full-visual hallucinations and I was gone from Earth.
This is not a usual reaction people have to weed. I haven't tried DMT or other hard psychedelics like that, but this story is the closest I've come to something similar.
This guy I was seeing at the time got me to try weed, and he had just a small bong (water pipe) and I took a few hits, wasn't really feeling much yet from it. But then his friend comes over, and he brings this huge bong, one of the 2-foot tall kinds and they had ice cubes in it and everything, and we started passing that around.
I didn't even take a full drag off this thing, I just cleared the smoke in it left by the other guy. Instantly I felt nauseous, and then after that, I was just gone.
What I was seeing in front of my eyes was an infinite 3D grid of colorful spheres, tiled out as far as I could see. I didn't have a body. I could see, but I couldn't move my "head", my vision was locked and staring at this grid of spheres. I could feel my eyes and knew the difference between opening and closing them, but it didn't matter, I was seeing these spheres all the same whether my eyes were opened or not. The real world was just gone, I was in this place now.
I immediately got some crazy ideas in my head, like: the simulation has ended, the Earth has been destroyed, and what I was seeing now were a bunch of other simulations, each sphere being its own separate universe. And that the people who were running these simulations were now studying the end results of ours that had just ended.
Occasionally I'd see a "screen" appear, a window where I could look through and see the real world, and I saw my friends looking in at me and asking "Are you okay? Do you need some water?", again and again on a loop. I interpreted this to be like video clips being pulled from the simulation for study by whoever it is that was running the simulation; that it wasn't "real" anymore, just a video clip, and it was repetitive with my friends asking me over and over again.
I could not speak out loud.
I could think to myself, and I could hear my thoughts just fine, but I just could not talk out loud. At least not on purpose. Occasionally I would manage to say something, and I could feel my throat vibrate and hear my voice, but I never knew when it would happen, and what I'd say would be just whatever random train of thought I was currently on in my head.
Sometimes I could manage to scream, and this would finally get a reaction out of my friends, who would finally say or do something different instead of just repeating the same questions over and over again.
When I'd struggle to get out of that place, I'd get to see the real world, only it was spinning in front of my eyes quickly as though I were shitfaced drunk on alcohol, and when I'd give up and relax I'd be back in colorful land seeing this grid of spheres once again.
It felt like I was there for an eternity.
I would've eventually just given up, relaxed, accepted my fate, etc., except there was a constant auditory tone that was ringing in my ears the entire time which kept me on edge and I couldn't fully just relax into it.
Eventually, I started to come down. I saw the spinning world again, only this time it was sticking around longer than before, and I started to remember how I had gotten myself into this situation. At this point I realized I was now standing on my feet and twirling in circles to keep up with my spinning world. I still could not speak, but I raised a finger in the air as if to signal "ah ha!" and that I realized my situation and that I'm on my way back down to Earth. Earlier in this 'trip', my friends had me pinned on the ground for my own safety and I scratched one of their arms for not believing they were even real during the trip.
Crazy stuff! The closest visual to this I've seen on the Internet is Indra's Net but really I've never seen anything else quite like it since.
I've never had such a reaction from weed since then, and tbh it kinda scared me off trying it again for another couple of years. By that stage all I'd ever tried was alcohol and I never contemplated such crazy ideas of simulations or things before this.
So when I studied the hexogonal patterns I see on weed now, what started to emerge from "behind the veil" looked an awful lot like the infinite grid of spheres and I noped right back to reality instead.
Unrelated to the above stories, but an interesting story nonetheless.
One day I was in a car driving down the highway, and I was chiefing on a weed vape pen, when suddenly I lost my depth perception to a certain degree.
The other cars on the road ahead of me started to appear as flat, 2D cardboard cut-outs, like those you might find at a shooting gallery. The cars still had reflections, highlights and shadows, to convey the illusion of 3D depth, only the car as a whole looked like a flat 2D sprite.
The 2D cards did still have relative depth compared to others, like, I could tell the difference between a car further ahead on the road compared to one closer to me; just each individual car, itself, was a flat sprite to my eyes with no localized depth to it.
I found it rather interesting and studied the rest of my visual perception to understand how it all worked. Like, way way off in the distance, there were some mountains covered in trees, only the whole mountain looked like a flat painting. It was so far away, that there was no panoramic effect as the car drove closer, it all just looked flat, like it was painted on, like the skybox of a videogame.
The cars nearby had relative depth, but far away, the horizon was flat. I thought, "where is the dividing line at? How far out do things stop having depth to them and it all looks flat on the horizon?" I estimated the line to be about 60 feet in front of me. Cars closer by than 60 feet, I could tell how far each car was from me and from the other cars; further out than that, everything may as well just be a flat matte painting on a wall, there's no more depth perception to be had at that distance.
I continued to study my perception in this state of mind and came up with the following ways to describe it:
And then imagine you have never left this room your entire life. You've never moved from that location, you've never turned your head. Instead, the paintings on the walls change and the actors come and go and change shape and form to make up your immediate environment. This was more or less what it "seemed" like in this moment.
I've written a lot of crazy stuff above, but don't worry, I don't take any of it too seriously! In my normal daily life I'm still a skeptical, science-minded kind of guy, and I even considered myself an Atheist for a good 10 years of my life, in between being raised a Christian from childhood and then re-discovering God in my own way in 2018.
All I know about the Universe is that I don't know anything about the Universe.
I like to dabble and explore my mind, and I fully acknowledge that this may be all it is, is my brain chemistry playing tricks. I can't make any claims that we're in a simulated universe or that gods or angels exist, or any kind of external magick like that.
Even from a material science perspective: our brains never see the Real Reality. We have eyes and ears and senses which feed electrical signals to our brain, and our brain does its best to simulate what might be going on in the external world. In that regard, we all do live in our own tiny little realities, and our own brains simulate our universes and no two people could ever know, for sure, whether what they call "red" is the same color as the other person.
There are surely some real dangers for your mental health if you delve into this kind of thing unprepared, or without the mental framework to handle it. Personally, I've always handled psychotropic drugs well, even during a "bad trip" where my external reality gets scary and out of control, I never lost sight of how I got there and I knew it was all mental and it too would pass and I'd be back to normal.
If there's interest I can talk about some psychedelic trip reports, too, though the above blog post is not really the same as "trip reports" and proper trip reports tend to be so random and chaotic, they don't even make sense to the reader, much like when somebody tells you about the crazy dream they had last night. Hopefully the above stories make some sense, though, and I explained some of it well.
Disclaimers: don't do drugs, etc., but if you do do them anyway, do your research and partake safely. Erowid is a good resource for that.
They say, of all drugs, that all they do is activate features in your brain that it's already capable of, oftentimes playing with your dopamine, serotonin or cannibinoid receptors, and that seasoned Buddhist monks (for example) can play in that space purely through meditation, just that it takes a while to master and drugs are a fast shortcut. A psychedelic trip can give you a peek through the veil and give you a glimpse at the nature of your perception of reality, but beware of unearned wisdom, and it's much safer to take the slower path there so you don't risk turning yourself completely crazy.
“The psychotic drowns in the same waters in which the mystic swims with delight.”
-Joseph Campbell.
I didn't find this documented very many places but it's possible to get a VNC server running for "remote desktop" to access and control your Pinephone display from your laptop.
Quick list of related technologies:
grim command.wf-recorder.Mobian already packages grim and wf-recorder
so these are just an apt install away, and these are documented
on Mobian's wiki. But wayvnc is not yet packaged in Mobian and you gotta build
it from source code yourself.
Follow the directions on the git repo, including cloning down the neatvnc and aml dependencies. The README has instructions to build it for Fedora and Arch but the Debian instructions are missing! I found by trial-and-error the dependencies I needed to install to build this program for Debian:
sudo apt install gcc meson ninja-build pkg-config libpixman-1-dev \
libdrm-dev libxbcommon-dev libwayland-dev
I ran the built binary like wayvnc 0.0.0.0 to start the server and connected
with the TigerVNC client from my desktop.
It has a couple of quirks to watch out for:
-r --render-cursor options to get the cursor to work. Thanks,
anonymous commenter!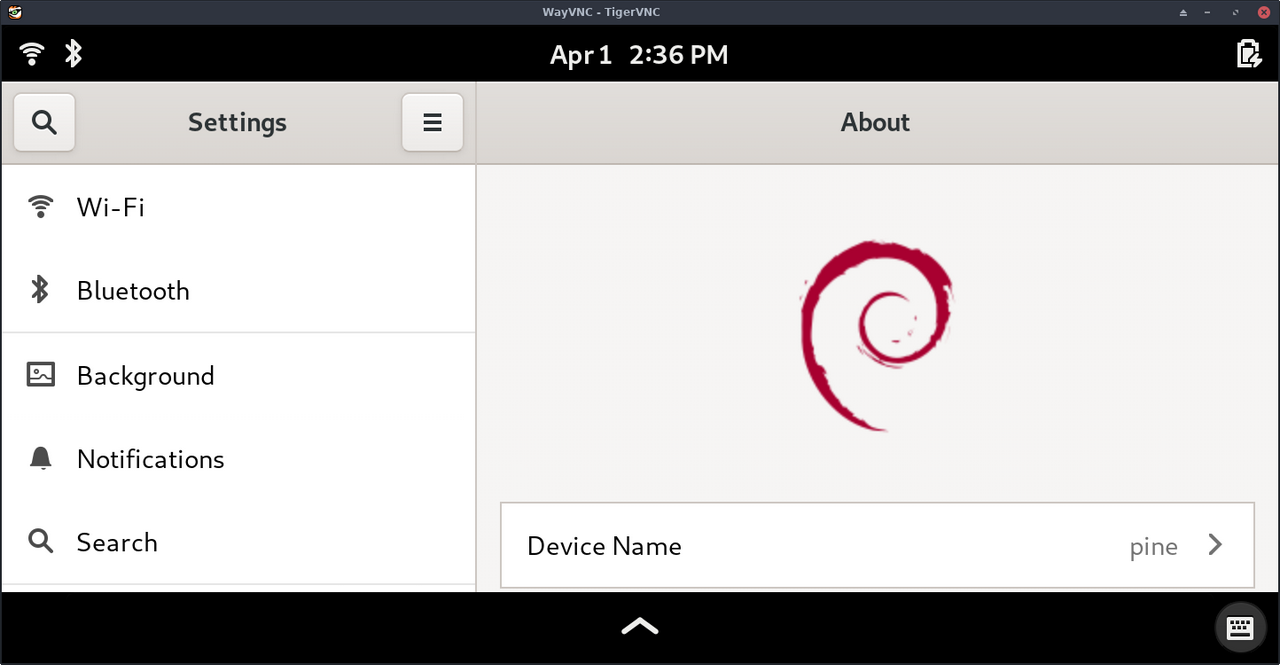
This is a general idea or concept I've had kicking around in my head about a way that a federated social network could work, wherein the user's own local device controls their identity rather than having a username on somebody's server.
To understand what I'm talking about, first let's run through what a federated social website even is. Briefly:
How would it look? With typical websites, there's a database and everyone has a user ID in it along with their email, username, bio text and whatever other details, and each website has their own database. What if you could move that user authentication to the client side? So instead of, "I log in as @kirsle with my password, so your back-end database can attest to my identity" it's instead "I'm telling you who I am, using a profile stored on my phone and not on your database."
The technologies to make this work on the client-side apps would be:
Now, what kind of site would this support? Not a site like Twitter or Instagram where users have a timeline and you host decades worth of pictures for them; these sort of sites require too much back-end state around user accounts.
Think instead of a site more like Reddit. Reddit is a "forum of forums" with tons of sub-communities but it's all on a centralized site. Imagine instead, that instead of subreddits on one site, each subreddit was its own separate server altogether, each server operated by different individuals on the Internet?
The server only hosts the forums and comment threads, not the user profiles. The user profiles are kept with the client app. If a server disappears, only its discussions are lost, not the users too.
So with my "self-authenticated client app" I could connect to a dozen different servers, each hosting their own communities, using my own local device identity to seamlessly authenticate to each server and post messages to their boards. The long-term state of each server, then, is only to do with the forum messages and less to do with maintaining profile pages and timelines. If a particular server decides to shut down and close up shop, nothing is lost, no user accounts were centrally tied to that server, users will just find replacements for their particular community discussions.
This idea is free for grabs, I don't think there's any money to be made from it, and I wouldn't mind if somebody made it a reality, I'll probably be too lazy to develop it myself. :)
The Adobe Flash Player is finally dead, and so the Flash animations I made back in high school don't play in Chrome anymore, so it was finally time to convert them to standard videos. Fortunately, there was such a thing as a "Standalone Flash Player" that could open my .swf files and it runs perfectly on Linux under Wine! So I just used vokoscreen to record the playback as a video to preserve these old animations for posterity.
The Kanian/Azulian War is the best animation I ever created in Macromedia Flash 5 when I was 15 years old. It features two classes of character I made up, the Kanians and the Azulians, going to war with each other and was inspired by various Newgrounds Flash cartoons that were popular in that era, such as Mario vs. Sonic.
Here is the Flash cartoon, featuring my awful voice acting. Read the full blog post to understand just what the f*ck is going on and who the Azulians and Kanians are, as I imagine this cartoon won't make much sense to people who weren't in my head at the time I made it.
There are many advantages to running a GNU/Linux operating system over something like Windows 10 (performance, privacy/lack of telemetry, security) but one under-appreciated aspect of Linux is that it's easy to repair.
It's like one of those old cars where you can pop the hood and get into the engine and repair it yourself, as compared to many of the modern vehicles out there which have sealed components and require special tools to get into and you need to take them in to a specialist.
Every operating system "breaks" sometimes. When Windows breaks, it boots in to a blue screen of death with a frowney face :( and it offers some "automated troubleshooting tools" which never work. They just spin for a while before saying: sorry! And how do you even begin to fix something like that? What if "Safe Mode" doesn't even load up?
For a specific example, it's been an annual tradition for me that my Windows 10 install gets "stuck": it can not install the new Windows 10 update due to "reasons" that it can't troubleshoot away. It'll do the whole pomp and circumstance: reboot, attempt to install, fail, roll back install, reboot, and tell me how it failed. Only to keep retrying every time I reboot from that point onwards. And I'm a rather light user of Windows (perhaps too much so), I rarely boot into it and even then only to play a few games like Skyrim.
Linux "breaks" sometimes, too, and maybe one day it doesn't boot into the graphical desktop because your nVIDIA drivers got borked somehow or your WiFi stops working after an update. What do you do? First, you can try booting into an older kernel from the bootloader menu; most distros keep the last couple of kernels as options for exactly this case.
Or you can boot into single user (text mode) and have a shell prompt logged in as root, so you can troubleshoot the issue: check log files, edit configuration, install or uninstall programs, and fix it yourself. Everything is very modular in Linux distributions, so it's hard to take down the whole thing. Very rarely is your bootloader so broken that you can't get get into a working single user mode.
Granted, this does require you to have some knowledge about how Linux works, but the great thing is there's lots of good documentation out there. Just google for "your distro name + thing you want to do". The Arch Wiki is great no matter which distro you run, though some small details may differ if you're using Fedora or Ubuntu, so prefer the wiki closest to your own distro of choice. Information from the Debian Wiki and Fedora Wiki tend to be broadly applicable to other Debian and Fedora downstream distros, like Ubuntu and CentOS.
Some of the most important skills to learn that gets you 90% of the way to fixing a broken Linux OS:
sudo reboot.In single user mode, basically only the Linux kernel and bash command line shell need to work, and it's very difficult for these to fail. No networking services start, no graphical desktop starts, and all video cards support text mode output regardless of any driver issues.
I basically never have to reinstall a Linux OS from scratch to fix any problems, and the times when I did, it was because I messed up and I learned to respect root privileges and double-check my commands. 🤣
or: 6 tangible ways that my personality suddenly shifted in 2018.
When people hear the words "spiritual awakening" they think of woo-woo magical things like Buddhism and enlightenment. But really a spiritual awakening can be explained in practical, ordinary terms as a moment in your life where you suddenly get a new outlook on the world.
In a spiritual awakening, you may suddenly realize that life is inherently meaningless, but that this is somehow a very freeing insight because it means you can create your own meaning. You don't have to be who you're expected to be but are free to be who you want, and you don't care what others think because you're also not even thinking about them. Or maybe a near-death experience, or grappling with your own mortality can trigger an awakening. It's really the same stuff: you'll be gone and all of your accomplishments forgotten, so what really matters in the world, what are we doing?
I had my spiritual awakening in early 2018, and in very practical terms, a lot of things changed in my personality quite suddenly:
But a BIG one is that I feel free to just not take the whole Human Game too seriously. What's the Human Game? It's all of the traditions and social norms we humans have come up with. The life plan of birth, marriage, kids, retirement; gender norms; the "9 to 5" work week; the scourge of social media on society; basically everything we do to distract ourselves from the fact that nobody knows what the fuck is going on or why the universe even exists at all.
It's all optional. You don't need any of it. You play along with the game because you find it fun for now. But it's just a ride. Some choose to go sit on top of a mountain for the rest of their days.
Since 2018 I've been more consciously choosing which parts of the game I play, and not worrying about the rest of it. I've been "de-googling" and don't, or can't, use many popular social networks or messaging apps. Not as many people can message me anymore, but that's just fine for me as an introvert. I can only manage so many relationships anyway, and the people who put in the effort to keep in touch are the ones worth keeping around.
Having 500 friends on Facebook never meant I had 500 friends.
Now, when somebody goes through a spiritual awakening, a common side effect is that they get some crazy thoughts in their head. They may then go down rabbit holes of woo-woo magical nonsense, which all suddenly takes on a lot more meaning, in search of answers, but I think there are no answers. Just people who've experienced something ineffable that escapes language, and they came up with lots of symbols and stories to try and communicate the feeling. None of it makes any sense until it does.
I can't describe what it feels like, just the practical effects it had on me in real life. And I'm not really out to 'convert' anybody, either, as I know that everybody is already where they need to be right now and everybody wakes up at their own pace. Maybe your spirit wants to experience what it's like to be you for a while before you can wake up and take the wheel. There's no words anybody could write that would 'pop your bubble', and when people try, that's how you get religions and spiritual woo-woo nonsense.
So be nice, have fun, and don't sweat the small stuff.
And it's all small stuff.
Signal is an end-to-end encrypted messenger app for smartphones that has been recommended by the likes of Edward Snowden and has seen an especially large influx of new users in recent months who are suddenly more concerned about Facebook or other tech companies reading or censoring their chat messages.
It's a fairly good app for what it does and it would probably fit the needs of your "average user" very well, but it doesn't work well for my needs and I still use Telegram in its place.
Now, I would like to use Signal instead of Telegram, because Signal's technology is more sound and the chats are truly end-to-end encrypted (where Signal Co. would be incapable of reading my chats even if they wanted to). Telegram in comparison uses some home-made cryptography (and you should never roll your own crypto) and their chats are not end-to-end encrypted by default, but Telegram does have some good quality-of-life usability features that makes it more appealing to me than Signal for now.
0.0066s.